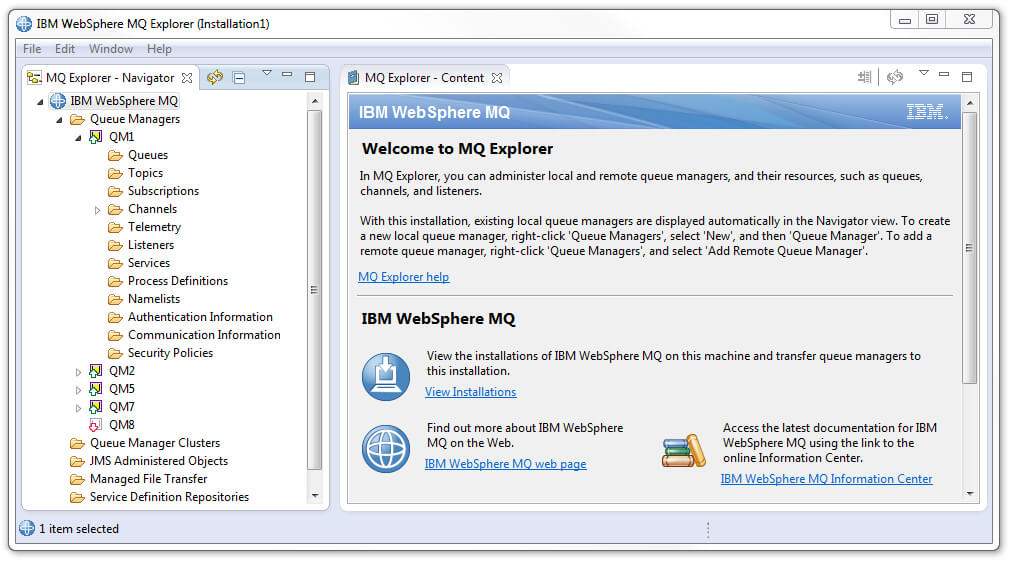
I will write some lines regarding migration of MQ servers.
Some people dont like the word "migration", "changing" because the environment is working like it is. I saw many application servers also that are using old version of software - for example Websphere Application Server v.6, which is out of support from long time.
The main problem with migration is development. Many applications that customers are using were bought and now they are without support also. The other problem is that nobody wants to change the environment because it is working for now.
This is wrong. With every new version of some product, the developer of this product is fixing main issues, bugs and making improvements.
But do not fall into details. When i migrated some MQ Clusters to latest version of MQ, I encountered problems.
AMQ9674: The channel `QM1.QM2.SSL` specified a weak or broken CipherSpec.
EXPLANATION:
The SSL or TLS channel `QM1.QM2.SSL` is configured to use a weak or broken
CipherSpec `TRIPLE_DES_SHA_US`. If the CipherSpec you wish to re-enable is an SSL V3.0 CipherSpec one step you will need to do is re-enable the protocol. This is done by editing the qm.ini file:
SSL:
AllowSSLV3=Yor setting the AMQ_SSL_V3_ENABLE=1 environment variable. Additionally, to re-enable the specific CipherSpec, you can edit the qm.ini file to provide the name of the CipherSpec you wish to allow to be used:
SSL:
AllowWeakCipherSpec=TRIPLE_DES_SHA_USor set the AMQ_SSL_WEAK_CIPHER_ENABLE=TRIPLE_DES_SHA_US environment variable.
IBM resources on the same subject:
- CipherSpec values supported in IBM MQ
- Deprecation: weaker cryptographic algorithms
- Specifying CipherSpecs
Clients that make use of CMP such as Message Broker Toolkit will hit an issue with the IDPWOS Authentication described above and therefore in order for them to work with WebSphere MQ V8 the following commands can be run to disable the new IDPWOS Authentication that is enabled by default in MQ8:
ALTER AUTHINFO(SYSTEM.DEFAULT.AUTHINFO.IDPWOS) AUTHTYPE(IDPWOS) CHCKLOCL(NONE)
REFRESH SECURITY TYPE(AUTHSERV)
These commands will remove the optional requirement for Username and Password authentication when connecting to the Queue Manager locally and then refresh the Authentication Service so the changes are picked up.
The reason this is required is that for a WebSphere MQ Version 8.0 Queue Manager the CONNAUTH CHCKLOCL attribute will be set to OPTIONAL by default. This means that user IDs and passwords are not required, but if they are provided they must be a valid pair, or they will be rejected.
Currently, the Config Manager Proxy will only pass a Username to MQ and therefore due to the new default, a MQRC 2035 (MQRC_NOT_AUTHORIZED) error will be seen when trying to connect to a Node using a WebSphere MQ v8 Queue Manager using the CMP.